Understanding Adversary-in-the-Middle (AiTM) Attacks
In recent years, Adversary-in-the-Middle (AiTM) attacks have surged to become the primary method for compromising organizations. They are notoriously difficult to detect because they do not "break" into a system; instead, they directly mirror legitimate authentication flows, even circumventing most Multi-Factor Authentication (MFA) controls.
How an AiTM Attack Works
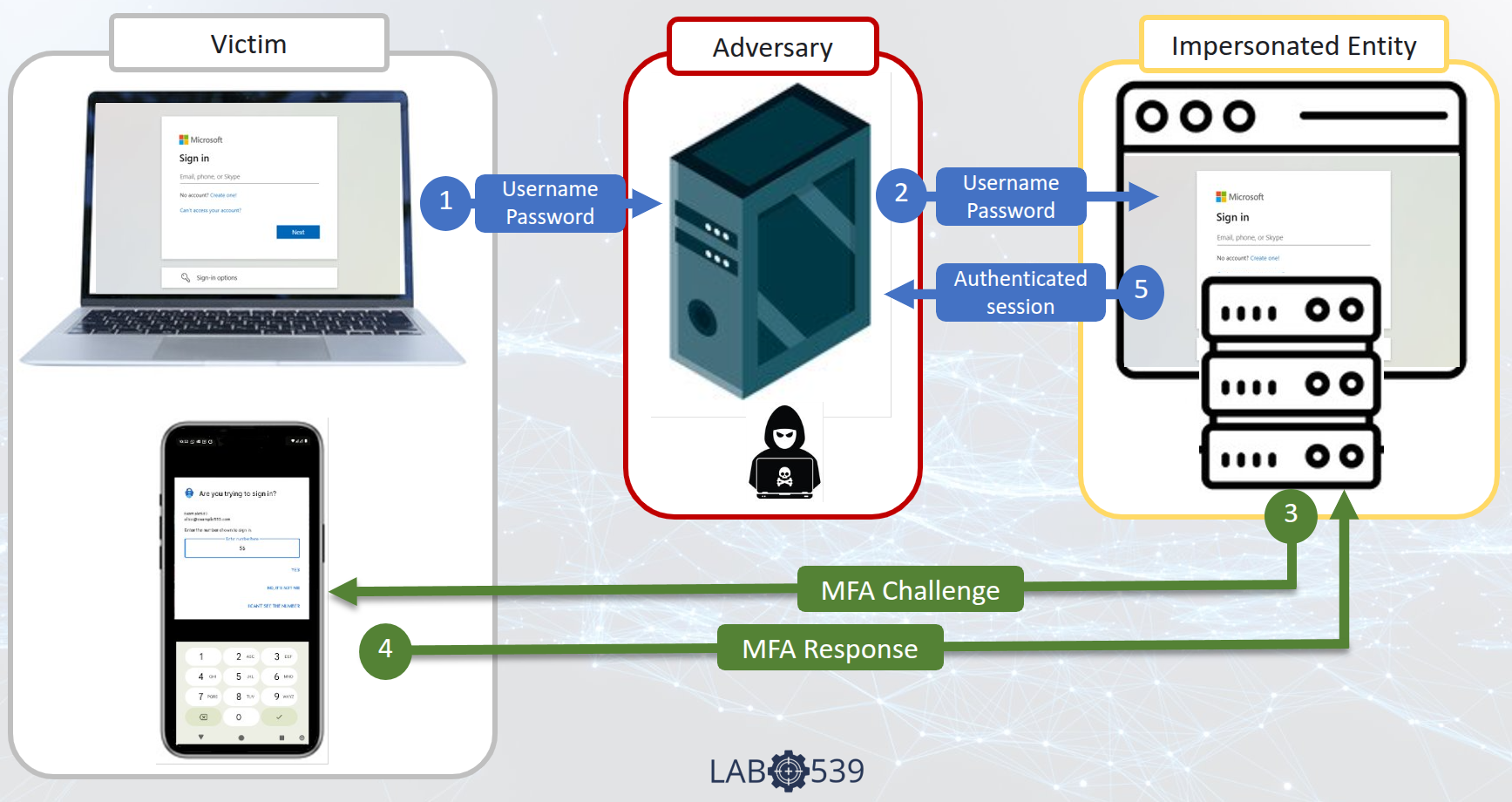
Unlike traditional phishing that simply captures a password for later use, an AiTM attack uses a live reverse proxy to sit between the user and the legitimate website in real-time.
The Technical Flow
- The Frontend Lure: A victim is lured to a phishing page (the frontend) that perfectly mimics a trusted service - whether it’s Microsoft Entra, Okta, Google, or a corporate VPN portal.
- Real-Time Proxying: As the user enters their credentials, the adversary’s backend infrastructure proxies them to the real identity provider (IdP) instantly.
- The MFA Bridge: If MFA is required, the IdP initiates a challenge. The attacker proxies this challenge to the user's browser or triggers the push notification the user is expecting.
- When the user responds - whether by entering a code or approving a push notification - they are actually authenticating the attacker's session.
- The Hijack: The moment the challenge is approved, the adversary captures the authenticated session ID (cookie). The password is secondary; the session token is the true prize.
The Psychology of the MFA Trap
A common misconception is that MFA is a "silver bullet." In an AiTM attack, MFA actually becomes a tool for the attacker.
Because the user is lured into a process they believe is legitimate, receiving an MFA push notification or a request for a code feels like a normal part of the security flow. The user approves the prompt because they expect it. Seeing a familiar prompt from an app like Microsoft Authenticator only reinforces the belief that they are on a legitimate site. They are unaware that their "secure" tool is confirming a session for a proxy engine.
The Vulnerability of 'Weak' MFA
Standard MFA (SMS, Voice, or App-based Push) is not "link-aware". It cannot distinguish between a direct login and one being funneled through an adversary's server.
The "Whack-a-Mole" Problem: Frontend vs. Backend
The security industry often falls into the trap of playing "Whack-a-Mole" with Frontend Infrastructure - the disposable phishing URLs that appear in emails and SMS.
- The Frontend (The Lure): Attackers can generate thousands of new URLs daily for near-zero cost. Blocking these is a purely reactive game of catch-up.
- The Backend (The Engine): This is the actual proxy engine (like Evilginx or Muraena) that performs the heavy lifting of authentication.
Our Philosophy: It is trivial to create a new frontend, but it is expensive and technically difficult to set up and maintain a backend proxy engine. At Lab539, we focus on identifying the backend infrastructure. By hunting the engine rather than the lure, we enable proactive defense that can kill multiple AiTM campaigns at once.
Post-Compromise: Automation and Persistence
Modern IdPs are exposed to the public internet, providing useful APIs that adversaries weaponize the moment a session is hijacked. Common post-compromise automations include:
- MFA Manipulation: Registering new attacker-controlled MFA devices to maintain permanent access.
- Email Rules: Creating silent forwarding rules to monitor sensitive communications.
- Data Exfiltration: Automated harvesting of files and sensitive data from cloud storage.
Defense Strategies
| Strategy | Effectiveness against AiTM |
|---|---|
| Passwords Only | None - Easily captured. |
| Standard MFA (Push/SMS) | Low - Easily proxied. |
| FIDO2 / Passkeys | High - Phishing-resistant hardware. |
| Backend Intel | High - Blocks the proxy engine before the user sees a prompt. |
Terminating Sessions
If you suspect a user has been victimized, terminating active sessions is an essential first step, although it may not be sufficient if the attacker has already established persistence via APIs.